Services
Cloud Technologies - getting
IT done.

Why Choosing an MSP with Disaster Recovery Experience Matters Selecting an MSP that brings specialized disaster recovery experience is a strategic decision that directly impacts your organization’s ability to withstand and recover from IT disruptions. Beyond customary managed services, an MSP with DR expertise understands the complex interplay of backup solutions, replication technologies, failover mechanisms, […]
Read this post
Comprehensive network procurement encompasses a strategic approach to sourcing the hardware, software, and services necessary to build and maintain an enterprise’s network infrastructure. It involves detailed planning, vendor assessment, cost analysis, and risk management to ensure that every component-from routers and switches to firewalls and wireless access points-aligns with organizational needs and technology roadmaps. This […]
Read this post
Strategic Planning for deploying WiFi Networks in Enterprise Environments Deploying WiFi networks successfully begins with meticulous strategic planning. The first step involves conducting an in-depth site survey to analyze the physical environment, identify potential interference, and determine optimal access point (AP) placement. Understanding user density, device types, and bandwidth requirements allows IT teams to design […]
Read this post
Comprehensive complete Protection with SOCaaS: The Next Evolution in Cybersecurity Security Operations Center as a Service (SOCaaS) represents a transformative shift in cybersecurity strategy, offering organizations complete protection across their entire digital habitat. Unlike traditional SOCs that require heavy investment in infrastructure and specialized personnel, SOCaaS provides managed, cloud-based security monitoring and incident response delivered […]
Read this post
Understanding the Essentials of IT Support Management Outsourcing Outsourcing IT Support Management involves delegating the duty of maintaining and managing an organization’s IT infrastructure to a trusted external service provider. This approach allows companies to leverage highly skilled professionals and advanced technologies without incurring the cost of building an in-house team. The scope typically includes […]
Read this post
Thorough IT Services UAE: Empowering Businesses with Advanced Technology Solutions The UAE’s digital ecosystem is evolving at an unprecedented rate, prompting businesses to seek tailored IT services that align with their strategic goals. IT Services UAE encompass a wide range of solutions, including managed IT support, cloud services, cybersecurity, software progress, and network infrastructure management. […]
Read this post
How Central Dubai Digital Transformation is Redefining Business ecosystems The digital transformation movement within Central Dubai is revolutionizing industries by adopting innovative technologies such as cloud computing, artificial intelligence, Internet of Things (IoT), and big data analytics. These technologies enable businesses to automate operations, gain actionable insights, and foster greater collaboration across departments and with […]
Read this post
Understanding Outsourced Network Management and Its Growing importance Outsourced Network Management entails delegating the oversight, maintenance, and optimization of IT network infrastructure to specialized third-party providers. This model allows businesses to benefit from expert resources without the need to maintain a full-fledged internal IT department. Providers like TechCloud IT Services L.L.C, trading as Cloud Technologies, […]
Read this post
Why Effective IT Support for SMBs is a Strategic business Advantage Providing robust IT support for SMBs is not just about fixing technical glitches; it’s a strategic pillar that supports operational efficiency and business continuity. SMBs frequently enough lack the extensive in-house IT departments typical of larger corporations, making outsourcing or partnering with specialized IT […]
Read this post
Complete autopilot Support Services Tailored for Enterprise IT Autopilot Support Services involve providing end-to-end assistance for Microsoft Autopilot deployments and management, focusing on simplifying device provisioning and lifecycle administration. At Cloud Technologies, we specialize in configuring Autopilot profiles that automate the out-of-box experience, enabling new devices to be ready for use with zero-touch deployment. Our […]
Read this post
Extensive Dubai Based IT Support Tailored to Your Business Needs In today’s competitive marketplace, having a dependable IT support partner in Dubai is indispensable. Dubai based IT support involves more than just fixing technical glitches-it encompasses managing your entire IT infrastructure to maximize uptime and ensure security. Cloud Technologies specializes in delivering end-to-end managed IT […]
Read this post
Transforming SOC to Use Sentinel: Unlocking Next-Generation Security Operations Adopting Microsoft Sentinel as the core platform for your SOC represents a strategic leap towards modernizing cybersecurity operations. Customary SOCs often grapple with siloed data sources, delayed incident detection, and manual response processes that impede operational efficiency. Sentinel addresses these challenges by consolidating security logs and […]
Read this post
Sentinel Integration with Google: Transforming Cloud Security Operations Microsoft Sentinel integration with Google platforms establishes a powerful synergy that elevates cybersecurity postures for organizations. Sentinel’s advanced SIEM functionalities, including AI-driven threat detection, automated response workflows, and real-time analytics, complement Google Cloud’s rich data ecosystem. This integration enables seamless ingestion of logs and events from Google […]
Read this post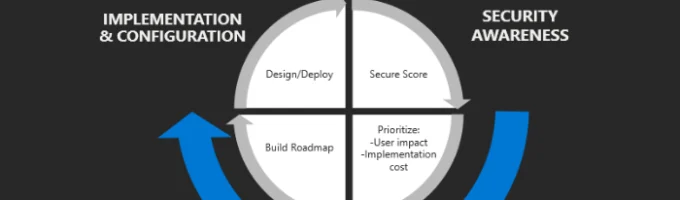
Understanding the Impact of Defender Score Improvements on Security Posture Improving your Microsoft Defender Score is more than just a metric-it reflects the robustness of your security strategy and operational readiness against cyber threats. The Defender Score, part of Microsoft secure Score, evaluates your organization’s security configuration and activity, assigning points based on the implementation […]
Read this post
Understanding the Pros and Cons of MSPs in Dubai’s Dynamic IT Market Dubai’s fast-paced business surroundings has led to a surge in demand for Managed Service Providers that can streamline IT operations. on the positive side, MSPs offer businesses access to cutting-edge technologies without the ample investment typically required to build an internal IT department. […]
Read this post
Unlocking the Potential of Microsoft Modern Workplace for Business Transformation The Microsoft Modern Workplace is more than just a set of tools-it represents a strategic framework that transforms traditional business operations into fully integrated, agile systems optimized for today’s workforce. At its core, this approach consolidates Microsoft 365 services such as Teams, SharePoint, OneDrive, and […]
Read this post